Healthcare cybersecurity: regulation, compliance, and risks
April 20, 2026 10 min read 5 views
Cybersecurity strategies are essential for maintaining operational continuity within a healthcare organization. An event such as a data breach can damage patient data, halt clinical operations, and create issues for leadership for months, resulting in legal, regulatory, and reputational harm. The financial impact of a data breach is real; the 2025 Cost of Data Breach Report from IBM found that the global average cost of a single data breach is $4.4 billion.
The uncomfortable question is this: do you have robust cybersecurity measures against today’s attacks, or does your security appear adequate only for compliance? Compliance is important; however, in the healthcare system, the majority of attacks occur through people, process gaps, vendor dependencies, and technical weaknesses. In this article, you will find information on how to translate compliance into daily security behaviours that will help you to lower your cybersecurity risks.
Healthcare cybersecurity key takeaways
- A robust cybersecurity framework establishes an overall structure; however, its success will depend on the level of consistency with which cybersecurity teams implement it in their daily operational workflows.
- To be resilient against real-world attacks, a secure infrastructure requires strong identity controls and robust monitoring interfaces.
- AI-compliance activities are at their best when they are associated with defined ownership, measurable SLA’s, and a commitment to reduce risk based on metrics, not through a checklist or auditing process.
- The cybersecurity incident response plan must be rehearsed and documented in accordance with clinical downtime procedures to ensure that containment does not disrupt the delivery of care.
The healthcare threat landscape and rising attack frequency
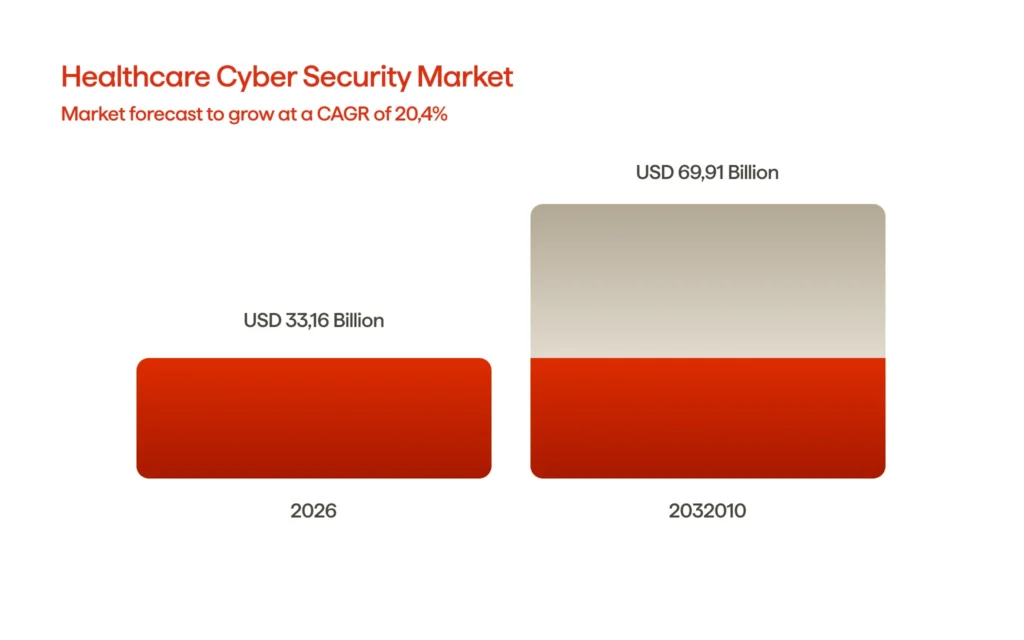
The attack frequency in the healthcare ecosystem is on the rise, as the number of potential attack surfaces outpaces the existing defensive structures that protect it. This trend can be demonstrated through funding: the cybersecurity market in healthcare is projected to grow from $27.46 billion in 2025 to $33.16 billion by 2026, or about a 20.7% compound annual growth rate (CAGR). Investment is aligned with risk considerations.
The healthcare industry has three main driving forces shaping its present-day landscape and future direction. Digitization (e.g., EHRs, patient portals, telehealth, connected workflows) is consolidating high-value identities and claims-grade healthcare data across more systems than ever before. At the same time, operational fragility (most had a legacy infrastructure, segmented ownership between their clinical and IT teams, and insufficient staff) has affected the efficiency of their patching and monitoring processes. Thirdly, dependency on ecosystems (billing vendors, cloud platforms, and device suppliers, etc.) creates 3rd-party pathways into core environments.
Ransomware, credential theft, and vendor compromise are some of the ways attackers are taking advantage of this situation. According to the Verizon DBIR, ransomware has increased by 37% and is involved in 44% of all breaches. In addition, the number of breaches involving third parties has doubled. This pattern can be traced directly to the healthcare industry’s reliance on outsourced IT and business associates.
Cybersecurity audits provide clarity to health care organizations by ensuring a durable commitment to safeguarding patients’ private information and adhering to constantly evolving cybersecurity standards. Rather than viewing the threat as one “big hack”, cyber threats are ongoing and will constantly put pressure on every endpoint; all identities, all third-party vendors; and every clinical operation.
Why compliance frameworks alone are insufficient
Compliance frameworks set minimum standards but do not address operational resiliency in healthcare environments. In many healthcare facilities, passing an audit does not secure the facility, because attackers do not attack a policy gap; they attack an operational gap through poor identity controls, inconsistent patching, permissive access, and third-party access. A collection of controls stored in a binder will not protect against credential compromise or ransomware attacks if teams are unable to quickly detect abnormal activity or isolate systems under duress.
Robust cybersecurity in healthcare must be viewed as a combination of lived behaviours and tested capabilities, not just an annual checklist or box to tick off. Successful cybersecurity protocols take into account how work is performed, specifically in relation to clinicians accessing systems, vendors connecting to systems, data movement, and the management of incidents that occur at 2 a.m. Without a strong cultural framework, staff will ignore controls to keep providing care, thereby creating exposure through well-intentioned workarounds.
Enhance research capabilities and optimize R&D strategies with tailored digital technology.
Core regulations: HIPAA, HITECH, GDPR, and state-level privacy rules
Despite being fragmented in scope, the direction of regulation in the healthcare sector has remained consistent: increased protection of health data and greater accountability due to the growing threats the sector faces. Successful compliance initiatives come from linking each healthcare regulation to clear control and ownership, and viewing audits as the basis for establishing a need for a strong cybersecurity program.
Covered entities and business associates who manage PHI/ePHI come under the scope of HIPAA compliance. The Security Rule allows the establishment of “appropriate and reasonable” administrative, physical, and technical safeguards to protect ePHI.
HITECH strengthens HIPAA’s enforcement capabilities and establishes formal notification requirements for breaches, including notifying affected individuals and, for breaches affecting over 500 people, notifying HHS and the media as well. HITECH also requires Business Associates to notify Covered Entities of any breaches at the BA.
GDPR governs all personal data located in the EU/EEA and considers Health Data as “Special Category” data requiring stricter conditions for processing. GDPR requires notification to the authorities of any breach within 72 hours in most instances and requires documentation of the breach.
In the United States, the privacy regulations at the state level are starting to go beyond HIPAA, and one example is Washington’s My Health My Data Act, which is focused on consumer health information that may not be covered by HIPAA regulation; it addresses issues of consent/ability to limit collection or sharing of such data.
| Regulation | Scope | What it forces in practice |
|---|---|---|
| HIPAA | PHI/ePHI for covered entities + BAs | Safeguards, access control, risk management |
| HITECH | HIPAA enforcement + breach notification | Timely breach reporting, BA accountability |
| GDPR | EU/EEA personal data, incl. health data | Special-category rules + 72-hour breach reporting |
| State laws | Consumer health data and broader privacy | Consent, minimization, vendor controls |
Building a culture of security in healthcare services
Treating security as an operational mode increases the longevity of modern healthcare cybersecurity compliance. According to the 2025 Verizon DBIR, approximately 60% of breaches involve the “human component.” Also, third-party compromises increased from 15% to 30%. This demonstrates how significant culture and processes are versus just tooling alone.
Leadership commitment and accountability
What leadership focuses on and supports is the basis of culture. The most successful programs assign an explicit risk owner for patient data and link security outcomes to operational performance measures, not just compliance measures. Practical steps include an incident management committee of clinical, IT, and revenue cycle executives; a designated executive sponsor of HIPAA Security Risk Management; and a RACI that defines who should approve an access request, approve patches, or resolve incidents as a way to eliminate the assumption that someone else is responsible and to be consistent in making decisions when a data breach risk is increasing.
Training, habits, and secure-by-default workflows
Individuals initiate most compromising pathways. Humans account for approximately 60% of all breaches, while the HIPAA Security Rule explicitly requires workforce members to receive training on security policies.
When it comes to effective training, the emphasis should be placed on operational aspects (not solely theoretical):
- Healthcare provider training should have a role-specific component for clinicians, front desk staff, billers, and IT administrators.
- Phishing simulation exercises should include micro-coaching (as opposed to punitive measures).
- Providing “secure default” options to minimize decision making: phishing-resistant multifactor authentication (MFA), least privilege access (LPA), auto screen lock, and managed passwords.
Incident readiness and “no-blame” reporting
The purpose of incident response in a healthcare provider organization is to maintain clinical continuity. The priority when a healthcare data breach occurs due to ransomware, account compromise, or incorrect system configurations is to maintain the availability of key healthcare services while limiting risk. Therefore, decisions must be pre-determined rather than improvised, including:
- Who is authorized to take systems offline?
- How are downtime workflows carried out?
- How do clinical teams communicate?
- Under what circumstances are external notifications made per regulatory requirements?
The earlier-mentioned report identifies the frequency of the “human element” in healthcare cyberattacks, making staff reporting the main input for detection. Additionally, adopting a “no blame” practice enables more frequent and faster reporting of suspicious emails, accidental disclosures, or abnormal device behaviour by staff members.
What this looks like in practice:
- Playbooks for ransomware, email compromise, and data exposure, mapped to clinical downtime procedures
- Regular tabletop exercises that include clinical leadership and operations
- Clear escalation paths and rapid containment steps (account lock, network segmentation, credential reset)
Third-party vendor and business associate management
Most risks in healthcare operations today no longer take place directly within the four walls. Electronic Health Record (EHR) extensions, billing partners, cloud hosting, managed service providers (MSPs), connected device vendors, and analytics tools typically affect patient workflows. Third-party involvement in data breaches has increased significantly over time. Therefore, vendor governance should be treated as a vital part of regular cybersecurity training rather than merely an afterthought of procurement.
Strong programs use vendor risk and access classifications as their starting point. For example, a business associate who can access ePHI or production systems may require additional management than a low-risk Software as a Service (SaaS) tool. Contractual agreements should support operational realities, including required security measures, approved audit rights, controlled subcontractors, and timely notifications of breaches in compliance with Department of Health and Human Services expectations.
On the technology side, the aim is to safeguard patient information by minimizing exposure: least-privileged access, conditional access, separate accounts, segmented connections, and automated offboarding. More mature teams will also continuously review vendor posture for high-risk vendors, rather than relying on yearly documentation.
FAQ
Turning compliance into everyday data security behavior
Regulatory compliance in healthcare settings is a floor, not a finish line. Healthcare cybersecurity regulations and frameworks help define what “good” should look like. Still, they don’t guarantee you can contain a cybersecurity incident at speed or prevent the small operational gaps that attackers exploit.
Many healthcare organizations that consistently protect patient data treat security as a part of providing care. This means taking ownership of security, adopting secure-by-default processes, rehearsing incident response plans, and consistently implementing vendor management controls. Strong cybersecurity practices are built in the same way clinical reliability is—by using standards, repetition, and continuous improvement. Compliance standards are therefore based on how an organization operates when culture and control reinforce each other; it becomes a product rather than something done just before an audit.
Want to learn more about key healthcare cybersecurity regulations and frameworks? Contact Avenga, your reliable partner in cybersecurity best practices.










