Cybersecurity in fintech: Protect sensitive data efficiently with Avenga
April 2, 2026 11 min read 10 views
A data breach is detrimental to a fintech firm’s growth. A breach doesn’t just put customer information at risk. It forces companies to report to regulators and brings shipping to a standstill while teams scramble to hunt down security gaps and patch up their defenses. This isn’t just a fintech problem, either. Take the recent case from Malwarebytes: hackers leaked a dataset linked to about 17 million Instagram users on a dark web forum. That exposed contact details, which are a prime material for phishing and identity theft.
Attackers do not always require passwords to inflict damage. When they breach fintech systems through weak processes or third parties, the cost of failing to take appropriate measures to secure data is quickly realized at a very public level. Keep reading to learn more about cybersecurity risks in fintech.
Fintech cybersecurity key takeaways
- Fintech faces some tough cybersecurity challenges. Every new API, partner connection, or quick software update just gives attackers more ways in.
- Top cybersecurity risks are usually predictable: account takeovers, gaps in API permissions, and risky third-party vendors.
- Absolute protection doesn’t come from a single tool. You need layers of defense, continuous monitoring, and a team ready to handle cybersecurity failures when they occur.
- The most innovative fintech companies must build security right into their development process. They use DevSecOps, automated tests, and lock down access so only the right people get in. That way, security grows as fast as the business does.
Fintech-specific threat landscape and attack vectors
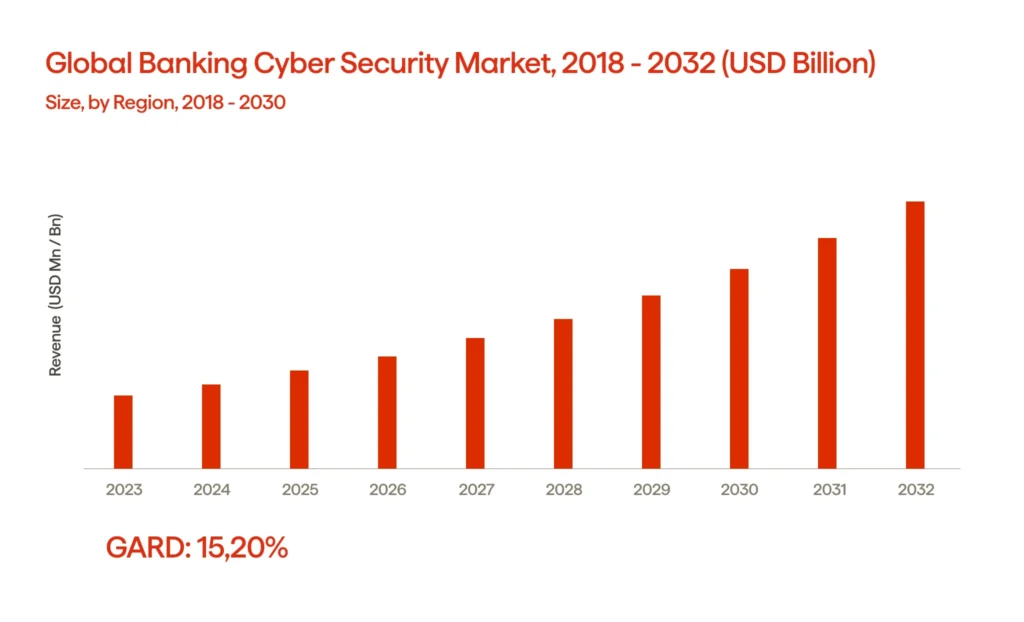
Fintech’s taken off fast, and honestly, that’s put a massive target on its back for cyber threats. Just look at the numbers, banks and financial firms worldwide spent about $12.1 billion on cybersecurity in 2023. By 2032, experts expect that to hit around $43.3 billion, which is some serious growth. For fintech companies, this makes sense. Modern apps lean hard on APIs, the cloud, and a bunch of third-party tools. That all adds up to a much bigger attack surface, so their security needs just keep climbing.
Most cybersecurity threats aren’t some wild new thing. It’s the same stuff hitting us again and again, credential stuffing, account takeovers, phishing, social engineering. They love going after support and ops teams. And API abuse is everywhere: broken authentication, replay attacks, too much data leaking out. Malware finds its way onto endpoints. Supply-chain attacks? Those get in through vendors or sketchy SDKs. Honestly, sometimes all it takes is one sloppy cloud storage setting or a bad IAM rule, and suddenly, you’ve got a hole big enough for a major breach.
So, what really works? Stick to disciplined security best practices and strong identity and access management. Keep monitoring everything, set up secure API gateways, and watch for fraud signals. And above all, have incident response processes ready, because attackers won’t miss a single weakness. Plan for them to poke at every link in the chain.
Evolving cyber threats targeting financial services and sensitive financial data
Fintech organizations face a nonstop barrage of new threats. APIs, cloud systems, mobile apps, identity providers, and a parade of outside vendors all end up handling sensitive financial data. Hackers don’t bother with movie-style break-ins most of the time. They just look for the weakest entry point and go for it. That’s why so many attacks look the same: easy, repeatable, and built to scale.
Account takeover (ATO) and credential abuse continue to lead the pack in fraud and security breaches. Attackers grab leaked passwords, hammer login pages with bots, and exploit weak session controls. So, what works? Start with phishing-resistant MFA. Add device fingerprinting, intelligent bot detection, risk-based authentication, and lock down your password reset flow. These steps actually move the needle.
You need tight support playbooks for your team, stronger verification steps when someone wants to change anything significant, dual control for risky actions, and tools that flag anything suspicious for your agents right away.
APIs remain a soft spot for most fintech companies. You see everything from broken authorization to data leaks, replay attacks, and insecure webhooks. To lock things down, treat your APIs like core products. That means consistent authorization checks, properly scoped tokens, rate limits, schema validation, idempotency, secure webhook signatures, and non-stop testing.
Third-party and supply chain security risks are a major pain point. Think SDKs, analytics tags, payment gateways, and KYC vendors. One weak link, and suddenly you’re dealing with a mess that spreads fast.
A lot of headaches come from cloud misconfigurations and identity drift,things like public buckets, giving out way too many permissions, or leaving secrets exposed. The fix is pretty straightforward: Build your infrastructure with code, lock your policies in as code too, rotate your secrets regularly, and keep an eye on your security posture every single day. And don’t just gather logs, you need to actually use them.
Reducing blast radius, continuously verifying IDs, hardening the “money-moving” flows, and assuming compromise are all consistent security measures that make detection and response as sophisticated as prevention. But let’s dig into this even deeper.
At Avenga, we deliver fintech cybersecurity solutions that empower banks and financial institutions to operate securely and efficiently in the digital era.
Regulatory compliance and data protection requirements (PCI DSS, SOC 2, GDPR, PSD2, regional frameworks)
The purpose of regulatory compliance in the fintech industry is more than just creating a document. The frameworks define specific security criteria and effective cybersecurity practices to reduce the frequency and severity of incidents across all types of fintech organizations engaged in the payment system and in collecting personal information.
The Payment Card Industry Data Security Standards (PCI DSS) are applicable whenever you store, process, or transmit cardholder data. Examples of these standards include complex controls on system and network segmentation, encryption, vulnerability management, logging, and network access controls. Tokenization is often used to reduce the number of systems that “touch” cardholder data by creating an isolated card data flow in and out of the card processing environment.
The Service and Organization Controls (SOC) 2 is a type of assurance report (not a law) required by many fintech vendors to complete the enterprise due diligence process. Evidence plays a major role in the SOC 2 report; it is intended to evaluate whether organizations have the necessary repeatable controls for security, availability, change management, access review, incident response, and vendor oversight.
The General Data Protection Regulation (GDPR) lays down the law on how companies handle personal data of anyone living in the EU or EEA. It’s not just about following rules for the sake of it,GDPR demands real discipline. Companies need to be smart about what data they collect, how long they retain it, and what they do in the event of a breach. They also have to take their vendor contracts seriously. Bottom line: organizations are on the hook to take solid technical and organizational steps to keep people’s data safe.
Payment flows in Europe are affected by PSD2, which allows third-party providers to access payment methods beyond the original direct-debit scheme. Payment flows will now include real-time or “instant” payments with 24/7 settlement. Therefore, payments will be completed sooner because there will be no batch latency, making the entire shopping process more efficient. But here’s the flip side: when fintechs use open banking APIs, they open the door to more cyberattacks. Less friction means more chances for threats to slip through. So, you need strong customer authentication, locked-down APIs, and sharp fraud monitoring and audit systems, no way around it.
| Framework | Primary focus |
|---|---|
| PCI DSS | Card data security controls |
| SOC 2 | Auditable operational controls |
| GDPR | Personal data privacy and protection |
| PSD2 | Payment security and authentication |
| Regional frameworks | Resilience, reporting, third-party risk |
Resilience is becoming a top cybersecurity goal as regional frameworks (such as operational resilience regulations) place more emphasis on third-party ICT risk, testing, and incident reporting.
API security in open banking and embedded finance
APIs enable open banking and embedded finance; therefore, your product’s overall safety depends on its request paths. When financial technology apps extract account data from aggregators, create payment requests from a bank account, or integrate a loan into a transaction at checkout, they are transferring high-value customer information and funds through interfaces that can be evaluated at machine speeds. The substantial security risks to numerous accounts could result from a single failed authorization check.
The most prevalent type of failure is object-level authorization, meaning a user has passed authentication. Still, the API fails to ensure that the authenticated user has access to the specific resource ID they are attempting to access. As such, attackers can enumerate resource IDs and harvest information. Additionally, token misuse is a more common vulnerability, including long-lived tokens, overly broad access scopes, lack of consent boundaries, or weak refresh flows.
Practical controls that improve the overall security:
– Correctly use OAuth 2.0/OIDC with least-privilege scopes, short-lived tokens, PKCE (proof keys for code exchange) for public clients, and strong consent models.
– Use financial-grade design patterns such as mTLS (mutual Transport Layer Security), signed requests, and strict audience/issuer validation.
– Enforce schema validations, rate limiting, and idempotency keys on payments and implement replay protection for sensitive actions.
– Provide an API gateway in front of each API with centralized authorization, WAF rules (Web Application Firewall), bot detection, and consistent logging.
– Monitor for anomalies such as unexpected spikes in 401 errors, sequentially accessing by ID, unusual token refresh patterns, and webhook retries.
Simply said, security experts build APIs to make misuse difficult, noisy, and swiftly confined, assuming that security issues will be regularly verified. As integrations grow, that’s how you safeguard your fintech.
DevSecOps: strengthening security posture in CI/CD pipelines
Delivery pipelines need to be considered an attack surface by the fintech sector. The majority of breaches occur from leaked secrets, exposed dependencies, or accelerated changes that bypass the appropriate review phase, rather than a clever exploit. By embedding security controls into CI/CD pipelines, DevSecOps will help reduce standard failure modes in the fintech industry while concurrently improving security and increasing shipping speed.
Third-party and supply-chain risk is a huge pain point, think SDKs, analytics tags, payment gateways, and KYC vendors. One weak link, and suddenly you’re dealing with a mess that spreads fast. You need solid vendor due diligence, give out only as much access as people really need, segment everything, keep an eye on things nonstop, and be ready to cut ties at a moment’s notice.
Then there’s cloud misconfiguration and identity drift. Honestly, these are behind so many incidents that should never happen,public storage buckets, too many permissions, secrets showing up where they shouldn’t. The answer? Use infrastructure-as-code, lock in policy-as-code, rotate secrets, stay on top of your security posture every day, and don’t just collect logs,review them.
Strong, robust data security is the final result. You get regular checks, quicker remediation, and fewer “we shipped it and hoped” releases, rather than depending on hero reviews.
FAQ
Balancing fintech innovation with risk management and resilience
Trust is the engine behind fintech’s growth, and you build it by taking cybersecurity seriously,no shortcuts. Fix those weak spots hackers are always hunting for. Lock down your APIs and data pipelines. Don’t just talk about incident response; make it part of how you work every single day. That’s how you protect your fintech company: keep things moving fast, and never let security become a bottleneck.
Want to learn more about fintech security and strategies for safeguarding sensitive data? Contact Avenga, your reliable information security partner.