Supply chain security essentials: Cyber attacks and defensive strategies

March 16, 2026 11 min read
Modern cybersecurity has become vulnerable due to the complexity of supply chains. Although organizations have hardened their internal systems, a single compromised vendor, software library, or service provider can be leveraged by a large-scale supply chain attack to expose the organization. According to a recent analysis, the average cost of a data breach for an organization is $3.86 million per incident. In comparison, “Mega” breaches involving 50 million records or more can cost an organization upwards of $392 million. The numbers indicate the increasing scope/size of the “Blast radius” from supply chain risk.
As businesses become more interconnected, the tactics employed by attackers are evolving. Instead of forcefully accessing business networks by directly attacking the front door, many attacks have been made through the “back door” by exploiting trusted business relationships to undermine sensitive data, intellectual property, and the overall continuity and operations of an organization.
Key takeaways
- As a means of infiltrating their systems, cybercriminals are increasingly targeting suppliers and other third-party service providers.
- Compared with traditional system breaches, third-party software providers, cloud service provider(s), and/or application service providers compromise sensitive data far more frequently.
- Due to the increasing complexity and interdependence within many business supply chains, traditional security measures often fail to provide the necessary protection for the enterprise.
- To protect both national security and business continuity, a combination of sound risk management procedures, continuous risk monitoring, and cooperative responsibility amongst supply chain partners must be established.
Recent high-profile supply chain attacks and their impact on sensitive data
Recent attacks on supply chains demonstrate how even a single weak supplier can compromise an entire supply chain ecosystem. The cases described below demonstrate that attackers exploited suppliers or third-party integrations to circumvent perimeter security, making previously trusted systems the weakest link in the security chain by using them to compromise the supply chain on a massive scale.
Clop exploits Oracle E-Business Suite zero-day vulnerability
In early October 2025, Oracle sent a notice to its customers regarding ongoing attacks against Oracle E-Business Suite (EBS) due to unpatched versions on their networks. This warning is based on information from the Google Threat Intelligence Group, which reported that many companies had received extortion messages targeting company leadership, claiming they had hacked their way into EBS and obtained valuable data. These operations have been linked to Clop, a criminal operation based in Eastern Europe that has developed its own Ransomware-as-a-Service (RaaS) model, focusing on attacking large enterprises with high value and large amounts of sensitive data.
The attackers exploited a zero-day vulnerability (CVE-2025-61882) that Oracle made the effort to repair with an emergency fix on October 5, 2025. GTIG has verified that this vulnerability was used in conjunction with at least two previously exploited vulnerabilities (older), which were included in Oracle’s July 2025 Critical Patch Update. Many different industries were impacted by this attack, including Barts Health NHS Trust and GlobalLogic (businesses). The incident clearly demonstrates how even mature supply chain management solutions can fail to protect against breaches when timely security measures for complex business applications are not applied.
Salesforce hit with third-party hacks affecting high-profile firms
In August 2025, Google announced the large-scale theft of Salesforce customer data, which affected many of its clients. The initial wave of the attack, associated with the hacker group known as ShinyHunters, involved gathering publicly available information posted by businesses. However, within weeks, another and much larger attack would be executed. GTIG has attributed the second theft operation (the second wave of hacking) to a group identified as UNC6395 and has indicated that this group stole data from multiple Salesforce accounts/instances (a total of 42) over 10 days, from August 8 to August 18, 2025.
Third-party integrations, specifically with Salesloft’s Drift application, served as a conduit for spreading the supply chain attack, which originated from the compromised OAuth tokens. Companies that were negatively impacted included many of the largest providers in the cybersecurity industry, cloud service providers, and luxury brands such as Chanel and Pandora. Following these incidents, a similar breach occurred through Gainsight’s Salesforce Connector. The above attacks are examples of how interconnected SaaS ecosystems are and how the risk associated with a single supplier integration can be amplified throughout the ecosystem.
Qantas, WestJet, and Hawaiian Airlines hit in airline attack wave
Airlines began to be heavily targeted by data extortion attacks in mid-2025. An FBI warning indicated that the Scattered Spider group had been targeting the airline industry. Attackers breached Qantas’s call center through a third-party customer service platform, compromising 5.7 million customer profiles. WestJet and Hawaiian Airlines were also victims of similar attacks.
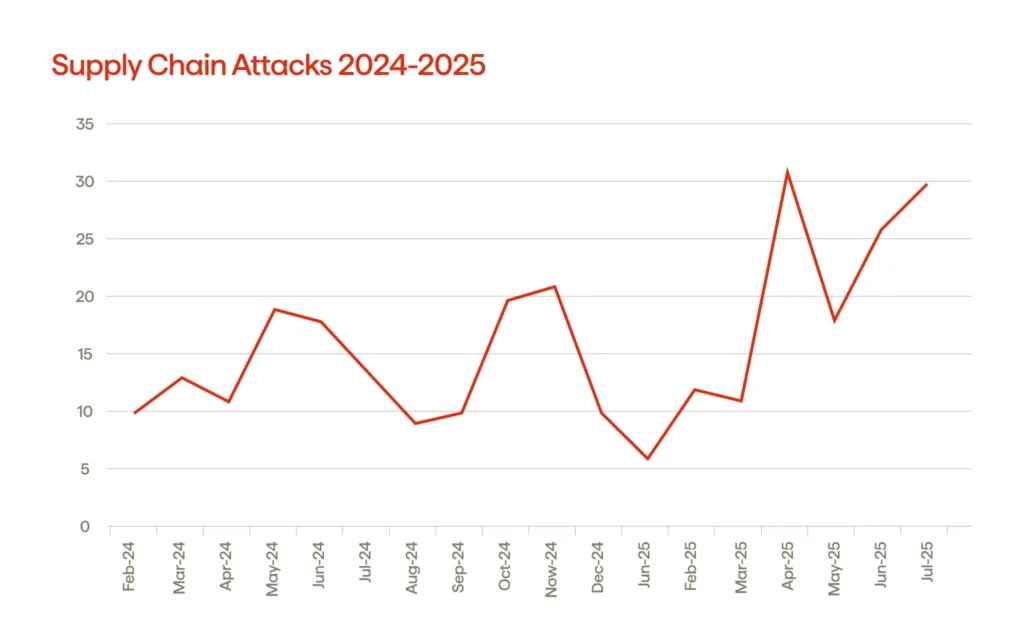
Attack vectors and cyber threat actor tactics targeting supply chains
An increase in the frequency of supply chain incidents regarding cybersecurity is not unexpected. Cyble’s dark web reports indicate that reports of supply chain attacks peaked in April 2025 at 31. Approximately 26 were reported every month involving supply chain compromise, or approximately twice the monthly average from January through March 2025. The change in attack method indicates a reevaluation of the attacker’s strategy, specifically in targeting the weakest or easiest links to access multiple downstream targets, due to the increased complexity in how companies operate within their respective ecosystems.
Third-party software exploitation
Enterprise platforms, plugins, and integrations that are widely adopted within companies are frequent targets of cybercriminal attacks. By exploiting security flaws in a trusted vendor, hackers can circumvent perimeter defenses, compromising the safety and security of many of the vendor’s customers simultaneously.
Compromised identities and access tokens
Attackers commonly exploit OAuth tokens, API keys, and service accounts. Once they have stolen these items, they can move horizontally across different systems without triggering conventional warning systems, thereby revealing the security weaknesses in a company’s identity and access controls.
Abuse of update and deployment pipelines
Cybercriminals embed malicious code within legitimate updates or products that are provided by authentic vendors. The fact that these updates/patches contain malware makes it difficult to detect, as they come from entities one would trust to supply products.
Social engineering of suppliers
Phishing emails and telephone calls targeting organizations that service privileged users have become increasingly prevalent. The problem with smaller vendors is that they tend to have less mature control processes, making them the most likely entry point for a more extensive supply chain compromise.
Living-off-the-land techniques
Attackers often employ built-in administrative tools to blend in with regular operations, rather than delivering overt malware. This strategy increases total impact by prolonging dwell time and delaying detection.
Software supply chain vulnerabilities and risks to intellectual property
The software development industry today is overwhelmingly reliant on third-party code, open-source libraries, APIs, and cloud-based tools. While this allows for faster time to market, it also increases the size of the cyber supply chain and the number of unknown risks that many organizations do not see. The more often you use an external dependency, the more opportunities an attacker has to gain access to your systems and steal your confidential and proprietary data.
The most significant threat to software security is losing visibility throughout the entire development lifecycle. Many development teams lack an inventory of all the components that come together to build an application. When a library or build tool with a vulnerability is developed by someone else and lacks appropriate oversight or management, it opens the door for someone to compromise it by tampering with the source code, potentially adding backdoors, or by obtaining proprietary algorithms and trade secrets without detection. All of these threats pose a significant risk to both the integrity and security of software, particularly when the affected source code is distributed as part of future software updates or through shared code repositories in a supply chain setting.
Due to inadequate oversight of CI/CD pipelines, improper access management, and a poorly managed vendor integration process, the potential for exposure is increased. Without strong management processes in place to identify malicious changes, an organization may not be able to detect them until after the IP has been leaked or further exploited for financial gain.
| Vulnerability area | What goes wrong | Risk to intellectual property |
|---|---|---|
| Third-party libraries | Outdated or malicious dependencies | Source code leakage, embedded backdoors |
| Build & CI/CD pipelines | Compromised automation tools | Tampered releases, stolen algorithms |
| Developer access controls | Excessive or shared privileges | Unauthorized access to repositories |
| Package repositories | Poisoned or spoofed packages | IP theft through trusted downloads |
| Vendor integrations | Weak security validation | Exposure of proprietary data |
Risk management strategies to mitigate supply chain cyber attacks
The foundation for implementing a successful program to mitigate against supply chain attacks is through effective risk management. With companies within the 21st century working globally, organizations are relying upon an ever-increasing number of software vendors, cloud providers, and service providers for their technology needs; therefore, security is no longer only about protecting the perimeter. Security must also be built into every aspect of a company’s supply chain.
It is through visibility that a company can create a security architecture. A company must understand which third parties have access to their network environments, what type of data is being processed/handled by each of those third parties, and identify potential security risks within the data that third parties process. Providing regularly scheduled assessments of vendor risks, setting security requirements in contracts, and ongoing monitoring of third parties enable companies to mitigate risks associated with supply chain attacks before a cyber attacker has an opportunity to exploit vulnerabilities.
Technical controls are just as important as administrative ones. The use of zero-trust architectures, multi-factor authentication, secure API gateways, and automatic patch management can reduce vulnerability to threats across connected systems. In addition, experienced security teams utilize similar resources to implement cyber essentials, such as encryption, code signing, and software bills of materials (SBOMs), which are used to monitor and track application dependencies and facilitate early detection of application tampering.
At last, the correct type of security tools enables you to utilize your incident response and threat intelligence feeds, as well as use automated processes that create alerts when anomalies are encountered. This helps organisations take immediate action against any potential security threats and protect the organisation from extreme loss while continuing operations.
FAQ
Strengthening supply chain integrity through proactive cybersecurity
Supply chain cyberattacks have transitioned from being viewed as rare instances/edge cases to being viewed as a significant trend. The consequences of these types of attacks extend well beyond the victimized companies; they threaten sensitive information, critical infrastructure, and even national security. Organizations that embrace the concept of being responsible for both the external elements of their supply chains and all the impacts associated with those elements will have a significantly more substantial advantage going forward than those that do not have a firm commitment to this approach.
Want to learn more about supply chain integrity and security? Contact Avenga, your trusted security company.